1000USD from KISA Bug Bounty
Fri Sep 28 2018 22:19:15 GMT+0900 (일본 표준시)
bughuntingpentestKVEbugbountyKISAwriteup
Table of Contents
KISA Bug Bounty Program?
KISA, the government owned organization in South Korea, provides bounty programs for any kinds of vulnerabilities in Korean softwares.
This bounty program is only applicable for Korean hackers who want to get paid for vulnerabilities. 😦
In South Korea, they assign cybersecurity identification number for reported vulnerabilities named KVE. KVE is pretty much identical with CVE except the fact that KVE is not visible to public.
Bounties for first try..
I've not participated to any kinds of bug bounties until this year because of my excessive workload at the workplace and spent my free time on studying other things apart from cybersecurity.
Somehow I got some time to review over softwares during my free time in the military base. I began analyzing some bugs in major Korean CMS softwares and some major websites which were applicable for the bounty program.
Most of Korean websites and CMS softwares are really vulnerable; which are prone to many kinds of exploitations. I had not much time to look over all things, so I decided to analyze some bugs for two hours per day (at maximum).
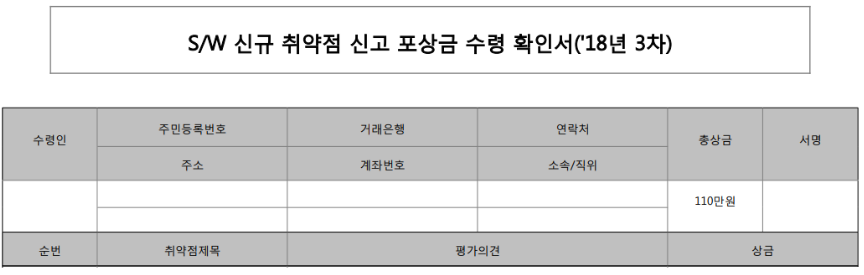
As a result, I received 1000 USD (1,100,000 KRW) for finding 6 different bugs in 6 days.
The most annoying part about this program is that one has to write bried details about every bug. This includes causes, findings and mitigations. At the end, writing details about vulnerabilities took me another 5 hours per bug.
Anyways, some vulnerabilities were not able to be fixed, while some were now fixed in 17th August and 22nd August respectively. (Some were also fixed in early September, but of course, I didn't get much information about it.)
Due to the regulations given by the bounty program, I can only publish details about vulnerabilities after 120 days from the patched date. So please come back later and check out the detailed information. 😃
Coming up next..
I am looking for other bounty programs. This is because:
I was not paid as much as I expected.
I don't want to waste time on writing 8 page documents whenever I find a new bug.
KISA bounty program did not seem to properly analyze the vulnerability; Some vulnerabilities were expected to have severe impacts on the service but I was paid much lesser than I expected.